The Essential SaaS Compliance Checklist for 2026


TL;DR: SaaS Compliance Is a Visibility and Governance Problem First
- SaaS compliance is expanding and getting harder to manage due to rapid app churn, global regulations, and limited visibility into SaaS usage.
- Responsibility is shared across IT, security, legal, and finance, however gaps form when ownership and coordination aren’t clearly defined.
- Lack of visibility is the biggest risk driver, increasing exposure to security incidents, compliance failures, and audit issues.
- Regulatory complexity is rising globally, with overlapping frameworks like GDPR, CCPA, HIPAA, and emerging AI regulations requiring continuous monitoring.
- A practical SaaS compliance program checklist starts with inventory and control, including app discovery, access management (SSO/MFA), encryption, and ongoing monitoring.
Managing SaaS compliance has become one of the most pressing responsibilities for IT, security, legal, and finance teams. Regulations are expanding across borders, and data privacy laws are tightening in nearly every major market. In addition, the pace of change inside the average enterprise SaaS portfolio (a 34% annual app churn rate) makes keeping compliance programs current harder than ever.
This guide breaks down the key regulations you need to know and provides a practical SaaS compliance checklist you can use right now.
What Is SaaS Compliance?
SaaS compliance refers to the set of security, privacy, and financial requirements that software-as-a-service companies and their customers must meet to operate legally and securely. It covers how a SaaS vendor designs and protects its platform, and how organizations using SaaS tools handle data and maintain regulatory adherence.
For SaaS companies, compliance obligations typically include securing customer data, maintaining access controls, protecting payment information, and demonstrating audit-readiness. For enterprises using SaaS tools, compliance involves managing which applications are in use, how data flows through them, and whether vendors meet required standards.
The two perspectives are closely connected. A SaaS vendor that fails a SOC 2 audit or violates GDPR requirements exposes every organization on its platform to compliance risk.
What is the difference between SaaS compliance and general IT compliance?
SaaS compliance specifically addresses risks and obligations that arise from cloud-based software subscriptions: vendor security certifications, data processing agreements, shadow IT exposure, and multi-tenant data handling. General IT compliance covers a broader scope, including on-premises infrastructure, hardware, and internal systems. Because most enterprise software is now delivered as SaaS, the two categories increasingly overlap.
SaaS Compliance vs IT Compliance
Who is responsible for SaaS compliance in an organization?
SaaS compliance is typically a shared responsibility across IT, security, legal, and finance teams—each covering different components of the checklist. IT manages application inventory and access controls. Security handles vendor risk assessments and incident response. Legal owns regulatory compliance and vendor agreements. Finance manages spend visibility and financial system access. Without clear ownership, compliance gaps are common.
SaaS Compliance Roles & Responsibilities
Why SaaS Compliance Matters
SaaS compliance protects your customers, your organization, and your ability to operate in regulated markets. However, non-compliance can result in financial penalties, while a single data breach or failed audit can trigger contract terminations, lost enterprise deals, and lasting reputational damage.
The financial penalties of non-compliance are substantial. For example:
- GDPR: fines up to 4% of annual global revenue or €20 million, whichever is greater
- HIPAA: civil penalties up to $1.9 million per violation category per year
- PCI DSS: card network fines, increased transaction fees, and, in severe cases, loss of the ability to process payments
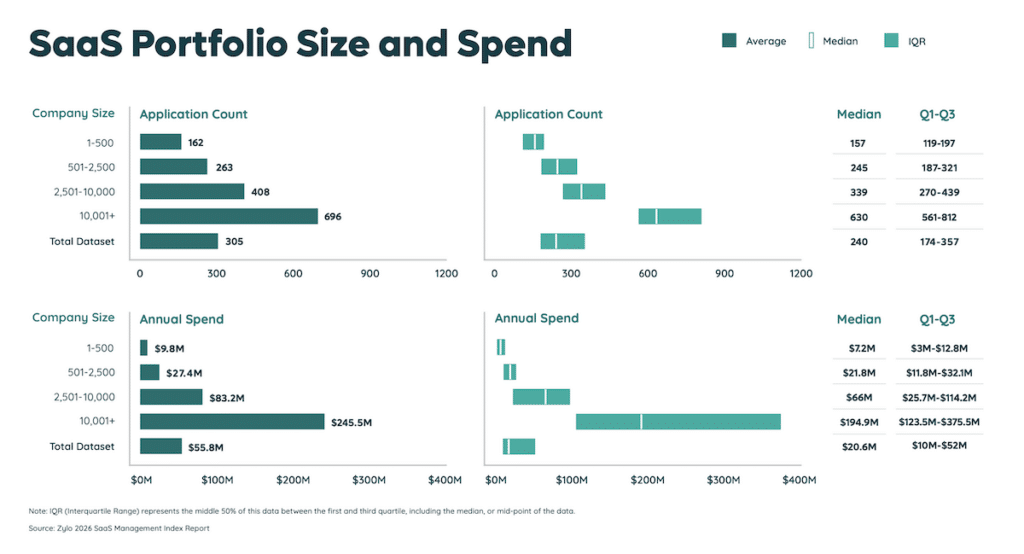
According to Zylo's 2026 SaaS Management Index, organizations average 305 applications in their portfolio—nearly 700 for large enterprises—and many underestimate that count by 200%. The scale of risk from this lack of visibility grows in step with SaaS adoption.
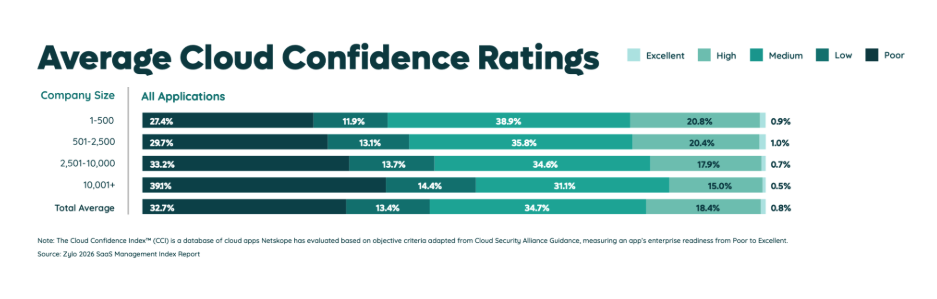
In the 2025 Gartner Magic Quadrant for SaaS Management Platforms, it states that organizations that fail to centrally manage SaaS life cycles are five times more susceptible to a cyber incident or data loss due to incomplete visibility into SaaS usage and configuration. In addition, the Index discovered that nearly half (46%) of applications carry a "Poor" or "Low" Cloud Confidence Index rating (Netskope risk score).
By implementing a SaaS compliance checklist, organizations can get full visibility of their applications, ensure each app meets compliance standards, and prevent financial, operational, and security risks.
Key Regulations and Standards for SaaS
The SaaS compliance environment spans security certifications, data privacy laws, financial requirements, and industry-specific frameworks. Understanding which apply to your organization is the first step toward building an effective program.
Security Compliance
The most widely adopted security compliance frameworks for SaaS companies are SOC 2, ISO 27001, and CSA STAR.
- SOC 2, developed by the American Institute of CPAs, evaluates how a SaaS company manages customer data across five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. Most enterprise buyers now require a SOC 2 Type II report before signing a software contract.
- ISO 27001 is an international standard for information security management systems. Achieving certification demonstrates that a SaaS company has implemented a comprehensive, audited framework for managing information security risks across people, processes, and technology.
- CSA STAR (Cloud Security Alliance Security, Trust, Assurance, and Risk) builds on ISO 27001 by adding controls specific to cloud providers and is increasingly referenced in enterprise vendor assessments.
For organizations evaluating SaaS vendors, Zylo's guide on security measures to look for in SaaS products outlines the certifications and controls to prioritize during vendor due diligence.
Data Privacy Compliance
Data privacy compliance requires SaaS companies to manage how personal data is collected, stored, processed, and shared. The requirements vary significantly by geography, and many organizations must satisfy multiple frameworks simultaneously.
International Data Privacy Laws
- The GDPR (General Data Protection Regulation) governs the processing of personal data of EU and EEA residents. It applies to any SaaS company that processes EU resident data, regardless of where the company is based. Key requirements include a lawful basis for processing, data subject rights, breach notification timelines, and data protection by design.
- PIPEDA (Personal Information Protection and Electronic Documents Act) governs commercial organizations in Canada that collect, use, or disclose personal information in the course of commercial activity.
- LGPD (Lei Geral de Proteção de Dados) is Brazil's data protection law, broadly aligned with the GDPR, and applies to any organization processing the personal data of individuals in Brazil, regardless of where the organization is based.
- APPI (Act on the Protection of Personal Information) is Japan's primary data protection framework, administered by the Personal Information Protection Commission and most recently amended in 2022.
- DPDP Act (Digital Personal Data Protection Act) is India's first comprehensive data protection law, enacted in 2023, with implementing rules continuing to roll out through 2026 and 2027.
- The Privacy Act 1988 is Australia's primary privacy legislation, covering government agencies and private organizations above specified thresholds, and was most recently amended in late 2024.
US State Privacy Laws
In the United States, no single federal data privacy law broadly applies to SaaS companies, but an expanding set of state laws creates a complex compliance landscape. The most widely adopted frameworks are:
- CCPA / CPRA (California Consumer Privacy Act / California Privacy Rights Act): the most comprehensive US state privacy law, granting California residents broad data rights and imposing obligations on businesses above certain thresholds.
- VCDPA (Virginia Consumer Data Protection Act): effective January 2023, follows a GDPR-influenced controller/processor model with no private right of action.
- CPA (Colorado Privacy Act): effective July 2023, adds a mandatory universal opt-out mechanism and was the first state law to regulate automated decision-making through rulemaking.
- CTDPA (Connecticut Data Privacy Act): effective July 2023, similar to the CPA with stronger protections for minors and consumer health data.
- UCPA (Utah Consumer Privacy Act): effective December 2023, the most business-friendly of the major state frameworks, with no opt-in requirement for sensitive data.
As of January 2026, 20 states are actively enforcing comprehensive consumer data privacy laws, with more than a dozen others currently advancing bills through their legislatures. Monitoring state-level changes is now a continuous compliance requirement, not a one-time review.
What's New in Data Privacy for 2026
Several regulatory developments are shaping SaaS data privacy obligations in 2026:
- The EU AI Act compliance requirements for high-risk AI systems took effect in early 2025, with additional obligations phasing in through 2027. SaaS products using AI for consequential decisions in hiring, credit, or critical infrastructure may face new conformity assessments and transparency requirements.
- India's DPDP Act is rolling out sector-specific implementing rules, making it increasingly relevant for SaaS companies operating in or serving the Indian market.
- Texas, Oregon, and Montana are among the US states with data privacy laws that took effect in 2025, expanding the compliance footprint for SaaS companies with broad consumer data exposure.
- The UK has continued evolving its post-Brexit data protection framework through the ICO, including updates to data transfer mechanisms affecting SaaS companies moving data between the UK and EU.
Financial Compliance
SaaS companies that process payments, manage financial data, or serve customers in regulated financial industries face a distinct set of requirements.
- PCI DSS (Payment Card Industry Data Security Standard) applies to any organization that accepts, stores, processes, or transmits cardholder data. For most SaaS companies, the preferred path is to route payments through a PCI-compliant processor and avoid handling raw card data directly. However, compliance responsibility still falls on the SaaS provider.
- SOX (Sarbanes-Oxley Act) applies to publicly traded US companies and governs internal controls over financial reporting. SaaS companies that are public, or that provide tools touching financial reporting processes of public companies, must maintain SOX-aligned controls over data access and integrity.
- ASC 606, the revenue recognition standard under US GAAP, directly affects how SaaS companies recognize subscription revenue. Finance teams must ensure billing systems and processes align with this standard and can produce compliant reporting.
Industry-Specific Compliance
Depending on the markets a SaaS company serves, additional regulatory frameworks may apply.
- HIPAA (Health Insurance Portability and Accountability Act) applies to SaaS vendors that serve healthcare providers, health plans, or other covered entities. Any SaaS company handling protected health information (PHI) must sign a Business Associate Agreement (BAA) with covered entities and comply with HIPAA's Security Rule, Privacy Rule, and Breach Notification Rule. Zylo's guide on HIPAA SaaS compliance covers these requirements in more detail.
- FERPA (Family Educational Rights and Privacy Act) applies to SaaS tools used by educational institutions receiving federal funding, governing access to and disclosure of student education records.
- FedRAMP (Federal Risk and Authorization Management Program) is required for SaaS companies selling to US federal agencies. It involves a rigorous authorization process based on NIST 800-53 controls and requires ongoing monitoring and continuous authorization activities.
- PCI DSS v4.0, which became fully required as of March 2025, introduced updated requirements for authentication, customized approaches to control implementation, and targeted risk analysis, replacing several prescriptive controls from the previous version.
SaaS Compliance and Audit Checklist
A practical SaaS compliance checklist helps IT, security, legal, and FinOps teams stay aligned on obligations and track progress. Specific requirements will vary based on which regulations apply to your organization. Here’s how to get started:
- Identify applicable regulations first
- Use strong authentication and restrict access
- Encrypt data in transit and at rest
- Monitor systems and log security events
- Document and test an incident response process
- Disclose how you collect and use user data
- Support user rights, including data access and deletion
- Use data processing agreements with vendors and partners
- Process payments through PCI-compliant providers
- Restrict and audit access to financial systems
Identify Applicable Regulations First
The most effective compliance programs start with a clear map of which regulations apply to your organization. Start by identifying:
- The types of data you collect (personal, financial, health)
- The geographies you operate in or serve
- The industries your customers are in
- Whether you're publicly traded or subject to specific contractual compliance requirements.
From that map, you can distinguish which frameworks are mandatory versus aspirational, and prioritize your investment accordingly. This regulatory inventory also forms the backbone of any SaaS compliance audit.
Jennifer Clark, Global IT Asset Manager at Hyatt, recommends starting with application visibility: "Building a library of all your applications should be number one on your goal list. You want to confidently say to auditors, 'This is my list of certified applications.'"
That clarity is harder to achieve than most teams expect. According to the 2026 SaaS Management Index, 60% of IT leaders report they lack visibility into all generative AI tools in use across their organizations. With shadow IT continuing to grow, SaaS visibility and inventory management are often a prerequisite for any effective compliance program.
"Building a library of all your applications should be number one on your goal list."
— Jennifer Clark, Global IT Asset Manager at Hyatt
What if your organization doesn't have dedicated IT staff to manage SaaS compliance?
Many small to mid-sized organizations successfully run SaaS compliance programs with limited dedicated resources. Cloud-based SaaS management platforms handle much of the heavy lifting on discovery, application inventory, and vendor risk scoring. You'll typically need someone to own the compliance roadmap, manage vendor agreements, and periodically review access controls. Assigning clear compliance ownership, even part-time, is more important than having a dedicated compliance headcount.
Use Strong Authentication and Restrict Access
Authentication controls are among the most fundamental requirements across SOC 2, ISO 27001, HIPAA, and virtually every other major compliance framework. Implement controls such as:
- Multi-factor authentication (MFA)
- Single sign-on (SSO)
- Role-based access control (RBAC)
Implement multi-factor authentication (MFA) for all users across your SaaS environment, and enforce single sign-on (SSO) wherever the application supports it. SSO reduces the number of credential sets in circulation and gives your security team centralized visibility and control over who has access to what.
Despite the clear mandate, SSO adoption remains low. Data from Zylo's 2026 SaaS Management Index shows that the average organization has secured just 21% of its applications behind SSO. For large enterprises with more than 10,000 employees, that number drops to 12%.
Use role-based access control (RBAC) to govern who can access what data and functionality, with access granted on a least-privilege basis. Conduct regular access reviews, at least quarterly, to remove access that is no longer needed due to role changes or departures.
Encrypt Data in Transit and at Rest
Encryption protects data from unauthorized access both while it moves between systems and while it sits in storage.Encrypt data in transit using TLS 1.2 or higher.
Encrypt data at rest using AES-256 or an equivalent standard. For SaaS companies storing sensitive personal or financial data, encryption key management is also a compliance consideration under GDPR, HIPAA, and several other frameworks.
Extend this review to your vendor portfolio, as well. When evaluating SaaS tools, confirming minimum encryption standards should be part of every vendor risk assessment within your broader SaaS management methodology.
Monitor Systems and Log Security Events
Continuous monitoring and logging give you the visibility to detect threats, investigate incidents, and demonstrate compliance to auditors.
At a minimum, security event logs should capture authentication events, privileged user actions, changes to system configuration, and data access and export events. Logs should be retained for a period that meets your most stringent regulatory requirement, often one year or longer for SOC 2, HIPAA, and FedRAMP.
A security information and event management (SIEM) system can aggregate and analyze logs across your environment, helping identify anomalous behavior and produce audit evidence efficiently.
For organizations managing large SaaS portfolios, SaaS application ownership data gives IT and security teams visibility into which teams are responsible for which tools, making it easier to assign monitoring responsibilities and close accountability gaps.
Document and Test an Incident Response Process
A documented incident response plan is a requirement under SOC 2, ISO 27001, HIPAA, and GDPR. But just having a plan isn’t enough—you also need to test it regularly.
An effective incident response plan defines roles and responsibilities, outlines detection and escalation procedures, establishes communication protocols for notifying affected customers and regulators, and documents post-incident review processes.
Regulatory notification timelines are strict. GDPR requires reporting a data breach to the relevant supervisory authority within 72 hours of discovery. HIPAA requires notifying affected individuals within 60 days. Build these timelines directly into your plan so they’re not discovered under pressure.
Test your plan at least annually through tabletop exercises or simulated incident scenarios. Document the results and update the plan based on what you learn.
Disclose How You Collect and Use User Data
Transparency about data handling is a core principle across GDPR, CCPA, PIPEDA, and virtually every major data privacy regulation. Users have a right to know what data you collect, why you collect it, how long you retain it, and who you share it with.
Your privacy policy should be written in accessible language, kept current, and clearly describe the legal basis for data processing under GDPR, the categories of data collected, user rights, and any third parties with whom data is shared.
For enterprises managing a SaaS portfolio, this obligation extends to vendor practices, as well. Reviewing vendor privacy policies and data-handling disclosures as part of a formal onboarding process is a standard component of any thorough SaaS compliance record.
Support User Rights, Including Data Access and Deletion
GDPR, CCPA, PIPEDA, and many US state privacy laws grant individuals the right to access, correct, and delete their personal data. As a SaaS company, you need both the technical capability and the operational process to honor these requests within regulatory deadlines.
GDPR requires data subject access requests to be fulfilled within one month. CCPA gives businesses 45 days, with an option to extend by an additional 45 days when reasonably necessary. Build a documented request intake and fulfillment workflow so that responses are consistent and timely.
Map where personal data lives across your systems so you can respond accurately. This includes data held by third-party processors, not just your own infrastructure.
Use Data Processing Agreements with Vendors and Partners
GDPR requires data processing agreements (DPAs) between data controllers and any processors they work with. HIPAA requires business associate agreements (BAAs) for vendors that handle PHI. Similar requirements exist under LGPD and several other frameworks.
Before onboarding any SaaS vendor that will process personal data on your behalf, confirm that a compliant DPA or BAA is in place. This applies to cloud infrastructure providers, analytics platforms, CRM tools, email service providers, and any other software that touches personal data.
Jennifer Clark of Hyatt captures the underlying challenge well: "One hundred percent, I would say the biggest SaaS risk is people. There's no shortage of employee ingenuity to work around the processes."
Part of addressing that risk is maintaining a current, auditable record of vendor agreements. SaaS application ownership reporting can help your team track which business units are managing which vendor relationships and where agreement gaps may exist.
Process Payments Through PCI-Compliant Providers
If your SaaS platform accepts credit card payments, PCI DSS compliance is mandatory.
The safest path for most SaaS companies is to handle payments through a PCI-compliant processor such as Stripe, Braintree, or Adyen, and avoid storing, processing, or transmitting raw cardholder data directly. This approach significantly limits PCI DSS scope.
If you do handle cardholder data directly, you'll need to complete a formal PCI DSS assessment and implement the full set of required controls, including network segmentation, access controls, and ongoing vulnerability management.
PCI DSS v4.0, fully required as of March 2025, introduced updated requirements for authentication, vulnerability scanning timelines, and customized control implementation, replacing several prescriptive controls from the prior version. Review your assessments and compliance documentation against the v4.0 requirements if you haven't already done so.
Restrict and Audit Access to Financial Systems
Limiting and logging access to financial systems is a requirement under SOX and a widely accepted best practice under every major security framework.
Only finance and accounting personnel with a documented business need should have access to billing systems, revenue recognition tools, ERP platforms, and financial reporting applications. Access reviews should occur at least quarterly, with immediate revocation upon departure or role change.
Audit logs for financial systems should record who accessed what, when, and what actions they took. These logs are frequently among the first items requested during external audits and regulatory reviews.
SaaS spend management tools give finance and IT teams visibility into software purchasing patterns across accounts payable and expense channels, helping to surface unauthorized or unreviewed access to financial systems before it becomes an audit finding.
Is there a SaaS implementation checklist for bringing new tools into compliance?
When onboarding a new SaaS application, a standard SaaS implementation checklist should include:
- Confirming the vendor's security certifications (SOC 2, ISO 27001)
- Reviewing the vendor's privacy policy and data handling practices
- Executing a DPA or BAA where required
- Verifying SSO and MFA support
- Assigning an application owner
- Classifying the application against your data handling tiers
Building this checklist into your procurement workflow ensures SaaS compliance is evaluated before a new tool goes live, not after.
How to Maintain SaaS Compliance Over Time
SaaS compliance isn't a project with a defined end date. Regulations evolve, your software portfolio grows, and your customer obligations change. Keeping compliance current requires ongoing attention across three areas:
- Staying updated on regulatory changes
- Running quarterly compliance reviews
- Managing compliance as you scale
Staying Updated on Regulatory Changes
Staying updated on regulatory changes means assigning a clear owner, whether a compliance officer, general counsel, or IT risk manager, to monitor developments in the jurisdictions and industries relevant to your business.
Running Quarterly Compliance Reviews
Running quarterly compliance reviews helps you catch configuration drift, access creep, and lapsed vendor agreements. Use these reviews to reconcile your application inventory against your DPA and BAA register, verify that SSO and MFA are enforced, and confirm that access controls reflect current employee roles.
Managing Compliance as You Scale
This is often the hardest part. Larry Hibbs, Technical Program Manager at the City of Aurora, Colorado, described their approach to ongoing SaaS compliance tracking: "The cycle we're looking at is finding [SaaS products] this year in Zylo, tracking them in Zylo, flagging them... we can see that this is a GASB-reported product."
That kind of systematic, ongoing tracking becomes increasingly difficult as portfolios grow. A structured approach to SaaS management methodology gives compliance, IT, and finance teams a repeatable framework for staying on top of vendor risk, data handling obligations, and regulatory requirements as your organization adds applications.
How often should we conduct a SaaS compliance audit?
Every organization should conduct compliance reviews on at least three timelines:
- Annually: review key controls, access rights, and vendor agreements. Frameworks like SOC 2 also require an annual third-party audit.
- Quarterly: recommended for high-velocity environments adding many new applications or employees each year — focus on access controls and vendor agreements.
- Immediately: any regulatory change, significant growth event, or data incident should trigger an out-of-cycle review.
Your SaaS Compliance Checklist Starts with Visibility
SaaS compliance starts with visibility. If you don’t know what applications are in use, you can’t enforce policies, assess risk, or prove compliance.
SaaS purchasing is decentralized, AI tools are entering environments unchecked, and portfolios change constantly. Without a reliable system of record, compliance becomes reactive—and gaps are inevitable.
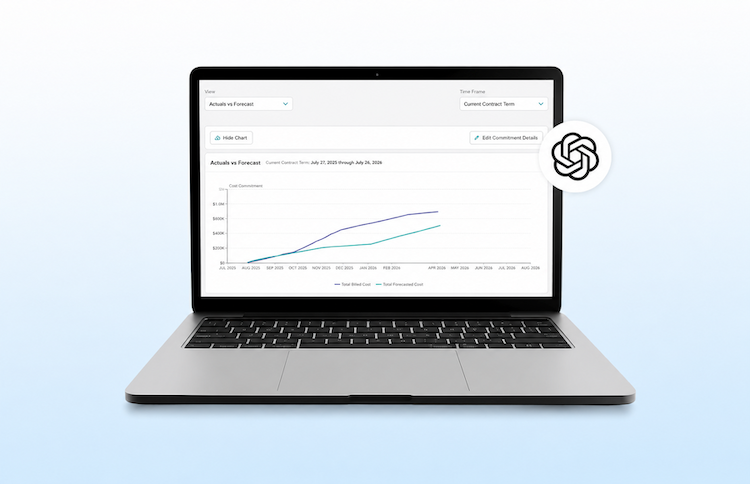
Zylo's SaaS management platform gives your team a complete, trusted view of your SaaS environment so you can reduce risk, strengthen governance, and stay audit-ready without manual effort. Instead of chasing down apps and contracts, you can focus on enforcing policies, aligning stakeholders, and scaling compliance with confidence.
Request a demo to see how Zylo helps you turn SaaS visibility into measurable compliance outcomes.