
The Best Software Asset Management Tools for SAM Teams in 2026
Table of Contents ToggleWhat Is SaaS Compliance?Why SaaS Compliance MattersKey Types...
Back
Back
Search for Keywords...
Blog

02/25/2026
Table of Contents
Though SaaS compliance can look like a policy issue, the primary concern is actually visibility. According to Zylo’s 2026 SaaS Management Index, the average large enterprise (10,000+ employees) has 696 applications in its portfolio. In addition, 46% of those applications are considered to have Poor or Low risk scores. These applications sprawl across decentralized teams, meaning IT, SAM, and Procurement teams have little insight into what tools are in use, where data flows, or whether security standards are being met.
This guide to SaaS compliance software gives you a practical framework for getting compliance under control. You’ll learn how to:
Whether you’re prepping for your first SOC 2, managing GDPR across a global portfolio, or navigating AI-related compliance concerns, you’ll find actionable guidance grounded in real-world enterprise data.
SaaS compliance refers to meeting regulatory, security, and contractual requirements when using cloud-based software applications. This includes adhering to data privacy regulations, security standards, industry-specific mandates, and license terms that govern how your organization stores, processes, and protects information within SaaS environments.
At its core, SaaS compliance ensures your software portfolio aligns with both external legal obligations and internal governance policies. It spans data protection frameworks such as GDPR and HIPAA, security certifications such as SOC 2 and ISO 27001, financial reporting standards, and license compliance requirements that prevent unauthorized software use or incurring overage penalties.
SaaS compliance protects your organization from regulatory fines, security breaches, and operational disruptions. Nearly half of the applications in the average portfolio carry Poor or Low Cloud Confidence Index ratings, introducing significant security and compliance risks. Without structured oversight, organizations face data exposure, contract violations, and audit failures that can result in financial penalties and reputational damage.
Compliance also enables business growth by establishing trust with customers, partners, and regulators. Organizations with strong governance frameworks can pursue new markets, demonstrate data stewardship, and respond confidently to audits.
There are several types of SaaS compliance organizations must prioritize, including:
Data privacy compliance governs how your organization collects, stores, processes, and shares personal information through SaaS applications. These regulations protect individual rights and establish accountability for data handling practices, with enforcement agencies imposing steep penalties for violations.
Security compliance ensures SaaS applications meet industry-recognized standards for protecting sensitive data, maintaining system integrity, and demonstrating enterprise readiness. Frameworks like SOC 2 and ISO 27001 provide objective criteria that help organizations assess vendor security posture before adoption and throughout the application lifecycle.
Financial compliance ensures accurate accounting for SaaS spend, proper revenue recognition, and adherence to procurement policies. To maintain compliance, organizations must:
SaaS sprawl complicates financial compliance when applications are purchased outside formal procurement channels. According to the 2026 Zylo SaaS Management Index, 81% of SaaS spend now originates from lines of business rather than IT. As a result, financial records are fragmented or incomplete, making it difficult to maintain audit-ready documentation.
“Building a library of all your applications should be number one on your list. You want to confidently say to auditors, ‘This is my list of certified applications.’”
License compliance prevents unauthorized software use, ensures adherence to vendor contract terms, and avoids costly true-up penalties during audits. Organizations must track license entitlements, monitor active users, and maintain documentation to verify that deployments remain within contracted limits.
According to Zylo’s 2026 SaaS Management Index, enterprises waste an average of $80.6M annually on unused SaaS licenses, with a median of $62.8. This license waste reflects both underutilization and inadequate license management processes. Organizations that maintain license positioning year-round avoid true-up costs at renewal and reduce spend by rightsizing entitlements based on actual usage.
Compliance protects your organization from legal, financial, and operational consequences while enabling growth through customer trust and market access.
| Category | Benefits of Compliance | Risks of Noncompliance |
|---|---|---|
| Data Security & Privacy Protection | Establishes baseline security controls to protect sensitive data from unauthorized access, breaches, and misuse. Improves detection and containment speed, reducing breach impact and cost. | Increased likelihood of data breaches. Higher exposure to unauthorized access and misuse. Average breach costs reaching $4.4M+ amplify financial impact. |
| AI Governance & Emerging Technology Risk | Enforces AI governance policies that monitor usage, protect company data, and control access to AI-powered tools. Reduces shadow AI exposure. | AI-related security incidents rise when governance lags adoption. Unmonitored AI tools increase risk of sensitive data exposure and regulatory violations. |
| Regulatory Compliance & Audit Readiness | Ensures adherence to frameworks (SOC 2, HIPAA, GDPR, etc.). Maintains documentation and controls required for audits. Supports continuous compliance tracking. | Regulatory fines, penalties, mandatory breach notifications, and legal liability. Increased audit scrutiny and reactive compliance efforts. |
| Financial Risk Management | Reduces unexpected fines, legal costs, and remediation expenses. Supports predictable SaaS spend and controlled contract management. | Escalating penalties and legal costs. Surprise expenses tied to compliance failures. Budget disruption from reactive remediation. |
| Reputational Protection | Strengthens customer trust by demonstrating strong governance and security posture. Builds credibility with enterprise buyers. | Loss of customer confidence. Deal delays or cancellations. Long-term brand damage that takes years to rebuild. |
| Customer & Market Access | Enables expansion into regulated industries and new geographies. Accelerates procurement cycles with documented compliance posture. | Restricted market access. Disqualification from enterprise deals requiring documented compliance certifications. Slower procurement approvals. |
| Operational Efficiency & Governance | Centralizes compliance monitoring and reporting. Aligns IT, SAM, and Procurement around structured governance processes. | Fragmented oversight across departments. Siloed management of SaaS tools. Increased operational friction and reactive firefighting. |
| Procurement & Renewal Strategy | Improves vendor due diligence and contract evaluation. Supports proactive renewal management aligned with compliance requirements. | Contract exposure to non-compliant vendors. Renewal risks tied to unvetted tools. Reduced leverage during negotiations. |
Compliance frameworks establish baseline security controls that protect sensitive data from unauthorized access, breaches, and misuse. Organizations that implement these controls reduce their exposure to security incidents and data loss.
In 2025, IBM’s Cost of a Data Breach Report found that the global average cost of a data breach reached $4.4M. Organizations with stronger governance experience faster detection and containment, which drives down breach costs. However, 97% of organizations lacking AI governance policies reported AI-related security incidents. Together, these figures demonstrate how quickly new technology can introduce risk when compliance practices lag behind adoption.
Non-compliance exposes organizations to regulatory fines, legal action, and reputational damage that can disrupt business operations and erode customer confidence. Today, AI is a prime concern. According to the Zylo’s 2026 SaaS Management Index, 93% of IT leaders express varying levels of concern about company data exposure through AI tools. Meanwhile, 43% cited exposure of sensitive company data as their biggest AI concern.
Regulatory enforcement has intensified across jurisdictions, and penalties for violations continue to escalate. Organizations that fail to meet data privacy obligations face fines, mandatory breach notifications, and legal liability. Reputational harm from compliance failures can result in customer attrition, lost deals, and diminished brand trust that takes years to rebuild.
“Playtime is over. We can’t afford to let AI grow unchecked. Structure is what keeps speed from turning into risk.”
— Jez Back, Cloud Economist and Global Offer Leader at Capgemini
Compliance enables business growth by demonstrating your organization’s commitment to data protection, security, and operational integrity. Customers, partners, and prospects increasingly evaluate vendor compliance posture before entering agreements, making certifications and audit readiness competitive differentiators.
Organizations with strong compliance programs can:
Compliance also streamlines procurement processes by:
Traditional governance models often struggle to address:
Regulatory requirements vary across industries, geographies, and data types, creating a complex compliance environment that requires continuous monitoring and adaptation. Organizations operating globally must navigate:
For example:
Each framework carries distinct audit expectations, documentation requirements, and penalty structures.
SaaS compliance operates under a shared responsibility model. Vendors secure the underlying infrastructure and application, while customers manage data governance, access controls, and compliance configuration. This division creates gaps in accountability when organizations assume vendors handle all compliance obligations or fail to understand which controls require customer implementation.
Vendors may achieve SOC 2 certification or ISO 27001 compliance. Still, these certifications do not absolve customers of their responsibility for data classification, user provisioning, or policy enforcement. As a customer, you must evaluate vendor security posture, review audit reports, and implement internal controls that align with your compliance obligations.
Compliance is not a one-time review—it is an ongoing operational discipline. Regulations evolve, vendors release updates, and business needs shift, requiring continuous monitoring to stay aligned.
SaaS applications change frequently, introducing new features, pricing models, and data flows that can impact your compliance posture. According to the 2026 Zylo SaaS Management Index, organizations add an average of nine applications per month, creating a constantly evolving portfolio.
Without continuous oversight, applications that were compliant at purchase can drift out of alignment as vendors introduce AI capabilities, modify data handling practices, or change contract terms.
Decentralized SaaS ownership creates compliance blind spots when business units purchase applications outside formal review channels. Our data shows that IT now manages just 15% of spend and 13% of applications. Meanwhile, shadow IT makes up 45% of applications in the average tech stack.
As a result, teams have limited visibility into:
Data fragmentation occurs when sensitive information is spread across multiple SaaS applications without centralized visibility or consistent governance. When organizations lack a unified system of record, compliance tracking becomes significantly more difficult.
Fragmented data environments make it harder to:
Limited visibility into application usage compounds the issue. Organizations often do not know which tools store sensitive data, how that data is classified, or whether vendors meet compliance requirements. According to the 2026 Zylo SaaS Management Index, 76% of IT leaders discovered AI-powered features or applications operating without IT’s awareness—highlighting how quickly unmanaged tools can create new, untracked data pathways that increase compliance risk.
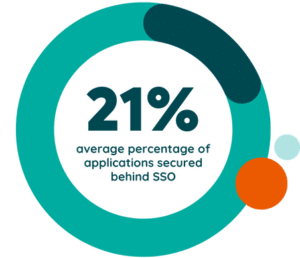
Without centralized identity management, organizations face an elevated risk of account compromise, data leakage, and unauthorized access to sensitive information. Employees who leave the organization may retain access to applications, former contractors may maintain credentials, and shared accounts may bypass audit trails that track user activity.
SaaS sprawl and rapid vendor updates create a dynamic compliance environment that requires continuous monitoring:
On average, the size of the average portfolio grows by 34%. This velocity makes it difficult to maintain compliance when governance processes cannot keep pace with adoption.
For effective SaaS compliance, follow these five best practices:
Start by identifying the regulatory, security, and contractual obligations that apply to your organization based on geography, industry, and data types. By conducting this assessment, you establish the compliance baseline that informs vendor evaluation, risk management, and governance policies.
For example:
Each framework carries specific requirements for data handling, breach notification, audit documentation, and vendor management.
Conduct regular risk assessments and gap analyses to:
Through these assessments, examine application security, data flows, access controls, vendor certifications, and internal governance processes.
Audit readiness requires:
Implement technical, administrative, and access controls that enforce compliance requirements across your SaaS portfolio. Controls should address:
Consider implementing:
Automate compliance workflows to reduce manual effort, improve accuracy, and scale governance as your SaaS portfolio grows. Compliance software centralizes vendor assessments, tracks certifications, monitors regulatory changes, and generates audit reports that demonstrate your adherence to security and privacy requirements.
SaaS Management Platforms like Zylo provide visibility into application inventory, risk scoring, renewal timelines, and usage data that support compliance oversight. These platforms integrate financial, identity, and application data into a single system of record, enabling IT, Procurement, and Security teams to manage compliance at scale across decentralized environments.
Maintain comprehensive documentation that proves compliance during audits, including:
By having audit-ready documentation, you can demonstrate governance discipline and reduce the time and cost associated with compliance reviews.
Organizations should centralize contract records, track vendor security posture, and document changes to the SaaS portfolio over time. This creates a defensible audit trail that shows compliance obligations were understood, controls were implemented, and monitoring occurred throughout the application lifecycle.
Compliance software automates vendor assessments, tracks certifications, monitors regulatory requirements, and generates audit reports that demonstrate adherence to security and privacy standards. The following list includes the top software provides that helps organizations manage compliance at scale.
While these aplatforms share common capabilities in audit automation and control monitoring, they differ in governance scope, privacy depth, and SaaS lifecycle visibility.
| Tool | Main Focus | Competitive Advantage | Best Fit For |
|---|---|---|---|
| Vanta | Security compliance automation across 35+ frameworks (SOC 2, ISO 27001, HIPAA, GDPR) | Strong automation engine with 400+ integrations for continuous evidence collection and real-time control monitoring. Accelerates certification readiness. | Cloud-first startups and mid-market organizations pursuing initial certifications quickly. |
| Drata | Continuous compliance monitoring and audit readiness across 30+ frameworks | Emphasis on real-time dashboards, personnel monitoring, and structured audit workflows. Strong visibility into control health and employee access compliance. | Security-forward SaaS companies that want operational visibility into control performance. |
| Secureframe | Compliance automation and integrated risk management | Combines automated evidence collection with built-in risk tracking, vendor assessments, and employee policy management to reduce audit prep time. | Growth-stage companies seeking centralized compliance workflows with integrated risk tracking. |
| OneTrust | Enterprise privacy, data governance, and AI-ready risk management | Broad governance platform with strong data discovery, consent management, regulatory intelligence, and AI governance capabilities. | Large enterprises with complex global privacy and regulatory requirements. |
| Zylo (SaaS Management Platform) | Enterprise SaaS inventory discovery, governance, and lifecycle management | Establishes a complete SaaS system of record across financial, identity, and admin data sources. Unifies spend, contracts, usage, ownership, and renewal visibility to reduce compliance blind spots at scale. | Enterprise organizations managing decentralized SaaS portfolios that require full application visibility before enforcing compliance controls. |
Vanta, Drata, and Secureframe automate:
OneTrust expands beyond audit automation into:
Most compliance automation tools assume:
For IT and Security leaders, this assumption is risky. If unknown applications exist outside formal review channels, compliance automation platforms can only monitor what they are connected to.
About Vanta: Vanta automates security and compliance workflows for organizations pursuing SOC 2, ISO 27001, HIPAA, and GDPR, among 35+ frameworks. The platform continuously monitors security controls, collects audit evidence, and streamlines certification processes.
Features and Competitive Advantages:
About Drata: Drata provides compliance automation for SOC 2, ISO 27001, GDPR, HIPAA, PCI DSS, and 30+ additional frameworks. The platform simplifies audit preparation by continuously collecting evidence, monitoring controls, and tracking compliance status across cloud and SaaS environments.
Features and Competitive Advantages:
About Secureframe: Secureframe simplifies compliance for SOC 2, ISO 27001, HIPAA, PCI DSS, GDPR, and 20+ additional frameworks by automating evidence collection, monitoring security controls, and managing audits through a centralized platform.
Features and Competitive Advantages:
About OneTrust: OneTrust is an AI-ready governance platform for privacy, risk, data, and compliance. The platform supports data discovery, consent management, vendor management, and regulatory intelligence across global frameworks, including GDPR, CCPA, HIPAA, SOC 2, and ISO 27001. OneTrust’s growing emphasis on AI governance that sets it apart from more narrowly focused compliance automation tools.
Features and Competitive Advantages:
SaaS Management Platforms like Zylo complement compliance tools by providing the complete application inventory, ownership data, usage insights, and renewal visibility required to enforce governance at scale. While compliance tools automate audit workflows and track certifications, Zylo helps organizations:
Compliance automation ensures controls are monitored, while SaaS Management ensures every application is in scope.
“Zylo has helped us with the ability to establish a methodical and reliable framework for SaaS governance. The Zylo platform provides us with a complete view of our software spend and associated products.”
— Ash Rai, Former Director of Software Asset Management and Vendor Relations at Adobe
Your organization’s SaaS compliance framework should include:
A SaaS compliance framework formalizes accountability, risk evaluation, policy standards, monitoring, documentation, and ongoing review across a growing application portfolio.
To establish a foundation for governance priorities, organizations begin by mapping regulatory and contractual obligations to their SaaS portfolio to identify:
A centralized inventory—capturing ownership, contracts, spend, and usage—creates accountability. Each application should have a defined stakeholder responsible for access, renewals, and compliance artifacts.
Documented policies establish consistent requirements for security reviews, data classification, vendor risk evaluation, access controls, and contractual safeguards. Intake workflows operationalize these standards before new tools are adopted.
Continuous monitoring integrates with identity systems, cloud infrastructure, and SaaS applications to track control effectiveness and vendor certifications. Automated evidence collection supports sustained audit readiness.
“We couldn’t keep absorbing surprises. Governance gave us control, but more importantly, it gave us foresight.”
Centralized records—such as inventories, risk assessments, certifications, approval logs, and data processing agreements—support internal reporting and provide auditors with defensible proof of governance.
Regular reassessment ensures controls remain aligned as SaaS portfolios evolve, vendors introduce new capabilities, and regulatory expectations change. Without structured review cycles, applications that were compliant at adoption can fall out of alignment due to feature updates, AI integrations, contract changes, or shifting data flows. Continuous review prevents control gaps and governance misalignment from developing over time and sustains audit readiness.
Clear roles and responsibilities ensure compliance accountability across IT, Procurement, Legal, Security, and business teams. Each function contributes distinct capabilities that together create a comprehensive governance framework:
Compliance must extend beyond IT and Security to become part of organizational culture, where every team understands its role in protecting data, managing risk, and adhering to governance standards. Achieving this requires:
Organizations that integrate compliance into procurement workflows, onboarding processes, and performance metrics create governance discipline that scales with growth. Training programs ensure employees understand compliance obligations, while dashboards provide visibility into risk, audit readiness, and governance outcomes.
SaaS compliance is evolving in response to new regulations, advanced technology, and shifting vendor strategies that introduce complexity and risk.
Regulatory frameworks are expanding to address AI, data privacy, and cross-border data transfers, creating new compliance obligations that organizations must navigate. Governments worldwide are introducing legislation that governs AI transparency, algorithmic accountability, and automated decision-making.
Organizations must monitor regulatory changes, assess how new laws impact their SaaS portfolios, and update governance frameworks to reflect evolving obligations.
In 2026, mature organizations are standardizing on unified control frameworks to bring structure and discipline to fragmented compliance efforts. Rather than managing regulatory obligations in silos, they anchor governance in a single control architecture that maps across multiple standards and jurisdictions.
Instead of maintaining separate programs for SOC 2, ISO 27001, GDPR, and HIPAA, these organizations design controls once and apply them across frameworks. The result is reduced operational drag, less audit fatigue, and a compliance model built to scale as regulations expand and enforcement intensifies.
As SaaS portfolios expand and AI adoption accelerates, automation is becoming central to how organizations maintain oversight. Modern compliance environments rely on real-time integrations across cloud infrastructure, identity systems, financial data, and SaaS applications. Controls are monitored continuously, and compliance posture adjusts dynamically as applications, configurations, and regulations evolve.
Governance functions are converging as well. FinOps, ITAM, Security, and Compliance teams are aligning around shared data and unified platforms as cost management, risk oversight, and regulatory accountability increasingly intersect—particularly under AI-driven and consumption-based pricing models.
A SaaS Management Platform plays a foundational role in this evolution by providing visibility into application inventory, ownership, usage, and contract terms. Enterprise-scale compliance requires governance that extends across decentralized purchasing channels and adapts as the portfolio changes.
Use this checklist to evaluate your organization’s SaaS compliance readiness and identify gaps that require remediation.
Maintain a complete inventory of all SaaS applications, including:
Conduct regular audits that verify:
Review security controls to ensure:
Centralize documentation that proves compliance, including:
Establish a cadence for ongoing compliance oversight:
SaaS compliance software protects your organization from legal, financial, and operational risk while reinforcing customer trust and market credibility—especially as SaaS portfolios grow and AI adoption accelerates. Sustaining that protection requires centralized visibility, defined ownership, and continuous governance across every application to maintain audit readiness at scale.
Zylo provides the system of record that strengthens audit readiness by delivering complete visibility into applications, ownership, spend, and contracts. Learn how Hyatt’s software asset management team stays audit-ready and maintains compliance with Zylo. Or request a demo to see how enterprise SaaS governance supports compliance at scale.

Table of Contents ToggleWhat Is SaaS Compliance?Why SaaS Compliance MattersKey Types...

Table of Contents ToggleTL;DR: SaaS Compliance Is a Visibility and Governance...

Table of Contents ToggleWhat Is SaaS Compliance?Why SaaS Compliance MattersKey Types...

Table of Contents ToggleWhat Is SaaS Compliance?Why SaaS Compliance MattersKey Types...
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |