Table of Contents
Adrian Dunne knows the potential downside to success. After more than a decade of successful growth and strategic acquisitions, employees at his company, NextRoll (formerly known as AdRoll Group) had also acquired an overabundance of SaaS applications and realized their need for greater visibility into their tech stack.
As NextRoll’s Senior Director for Global IT, Dunne’s role includes monitoring and managing the software and SaaS footprint across the entire organization.
But multiple teams at multiple locations owned multiple unique SaaS application instances, obscuring the oversight Dunne knew was necessary to a proactive IT security posture. “I’m the type of guy who wants to know about every single piece of software in my environment,” he says.
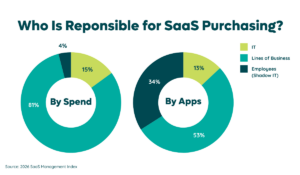
NextRoll is not alone in facing the challenge of shadow IT growth, which grows particularly quickly following growth, mergers, or acquisitions. These activities contribute directly contributors to unplanned decentralized software acquisition, but the issue is also widespread: Zylo data shows that more than 74% of SaaS spending now occurs outside of IT budget lines, owned by lines of business and individual employees.
As a result of more teams and business units spending directly on SaaS, the average Zylo customer initially underestimates the number of SaaS application within their org by two to three times.
More Data, Better Decisions
By utilizing Zylo’s SaaS management platform, Dunne and his stakeholders on teams like Finance and Security untapped a single, centralized view of all SaaS applications throughout every NextRoll team, regardless of location.
“We were able to use Zylo to get the critical data from financial transactions and gain a complete view of everything,” Dunne says. “It unmasked the rogue software spending that was sidestepping procurement processes or sitting on personal credit cards.”
Dunne says that Zylo’s direct integrations into financial systems also transformed the process of a software audit from an intensely manual spreadsheet-driven exercise into a streamlined, collaborative program that focused on curating, analyzing, and improving the data streams created by SaaS acquisition.
NextRoll reduced its number of duplicate applications by more than 53% within 12 months.
“It can be challenging to manage all the data Zylo presents and know where to begin,” Dunne says. “But once we had the tool in place, we were able to begin the exercise of cleaning everything up.”
With this data curated, streamlining app purchasing behaviors across the organization became possible. For example, NextRoll reduced its number of duplicate applications (those purchased by more than one employee) by more than 53 percent within 12 months of deploying the Zylo platform.
Visibility Creates Improved SaaS Security, Management
Zylo’s ability to make data about NextRoll’s SaaS application inventory fully visible enabled Dunne and line-of-business stakeholders to make immediate improvements to security and IT governance throughout the org chart.
To reduce risks caused by the proliferation of low-cost applications, Dunne’s and NextRoll rolled out a new procurement policy that eliminated reimbursement approvals for personally expensed SaaS app purchases.
Not only did this help stymie the growth of unique SaaS applications to NextRoll’s overall software inventory, it also helped improve the company’s cybersecurity and data protection stance.
“It wasn’t easy,” Dunne says. “It can be hard for people to fully realize the minute you sign in with your company email, you’re effectively giving away data. But we’ve driven that home and it’s working.”
NextRoll decreased the number of employees who expensed application purchases by 48%, creating a 22% reduction in the number of unique SaaS applications.
With the introduction of this process, Dunne and NextRoll decreased the number of employees who expensed application purchases by 48 percent in the 12 months. This process was also central to creating a 22 percent reduction in the number of unique SaaS applications.
For larger purchases, Dunne created a SaaS application review board with sequential approval, ensuring that no new application enters use within the business unless it’s first been reviewed by IT, security and compliance, then Legal for contractual terms, and finally Finance.
“No contract gets signed unless all four steps have happened,” Dunne says.
___
To learn more about how Zylo improves security through enhanced visibility and professional SaaS lifecycle management, request a demo of the leading SaaS Management platform today.
ABOUT THE AUTHOR

Cory Wheeler
As Zylo’s Chief Customer Officer, Cory is responsible for helping our customers drive ROI and SaaS Management success with Zylo. He helps companies of all sizes effectively discover, optimize, and govern their SaaS through Zylo’s platform and services. Prior to founding Zylo, Cory spent 15 years in finance and procurement, managing categories and sourcing teams at Arthur Andersen, BearingPoint, and both Takeda and Astellas Pharmaceuticals. He built the procurement organization at ExactTarget, and managed the integration with the Salesforce Marketing Cloud procurement organization in 2015. He and his family reside in Indianapolis, IN, where they can be found cheering for the Purdue Boilermakers and Chicago Cubs.