
FinOps Cost Optimization: How to Save on Cloud and SaaS Costs
Table of Contents ToggleTL;DR: FinOps Cloud Cost Optimization Expands in ScopeWhat...
Back
Back
Search for Keywords...
Blog

Table of Contents
Updated on April 21, 2026 with new data and in-depth CASB technology insights and best practices
Your employees are adopting cloud applications faster than your security team can track them. Every unsanctioned tool they sign up for opens another path for sensitive data to leave your organization without anyone knowing.
When employees adopt SaaS tools on their own, sometimes without IT approval, security teams lose visibility into where sensitive information goes and who can access it. A cloud access security broker (CASB) is designed to close that gap.
But CASBs don’t solve every problem that comes with managing a growing SaaS portfolio. Understanding what a CASB does, where it falls short, and how it works alongside a SaaS management platform will help you build a more complete cloud strategy.
A cloud access security broker (CASB) is a security policy enforcement point positioned between your organization’s users and cloud service providers. Leading providers include Netskope, Palo Alto, and Zscaler.
In 2012, Gartner coined the term to address the security risks that emerged as SaaS adoption accelerated, and the core function hasn’t changed. CASBs act as a gatekeeper for your cloud environment.
A CASB gives IT and security teams visibility into which cloud applications employees use and flags risky or unauthorized apps. It also consolidates multiple types of security policy enforcement into a single layer between your network and the cloud, including:
As SaaS portfolios grow, so does the attack surface. The 2026 SaaS Management Index found that the average organization now manages 305 applications and adds an average of 9 new tools each month. That volume makes it nearly impossible to enforce security policies manually, which is exactly the problem CASB technology was built to address.
Organizations need CASBs because cloud adoption has outpaced the security controls designed for on-premises environments. Traditional firewalls and network-based security tools can’t protect data once it moves to third-party cloud services, and employees routinely adopt new SaaS tools without going through IT.
Three trends are accelerating the need for cloud access security brokers:
Without a CASB, your organization has limited ability to detect which cloud apps are in use, whether sensitive data is being shared through unauthorized channels, and whether those applications meet your compliance requirements.
Shadow IT growth underscores the importance of a CASB. According to Zylo’s 2026 SaaS Management Index, expense-based SaaS purchasing grew 267% year over year. A smaller group of employees is driving more unmanaged spend, and many of these purchases bypass the security reviews that formal procurement channels provide.
AI tools introduce new data security risks, in which three in four IT leaders are concerned about, per Zylo’s survey. With artificial intelligence applications increasing in quantity by 181%, a CASB is crucial to ensure proper visibility and governance.
A CASB is an essential tool to help centralize all applications into a system of record—no matter who brought it into the organization.
In 2025, IT was responsible for just 15% of applications and 13% of SaaS spend, leaving a considerable blind spot. Decentralized software purchasing by employees and lines of business limits IT and Security’s visibility of your organization’s portfolio.
Cloud access security brokers are built around four core capabilities, often called the four pillars of CASB. These pillars work together to give security teams control over cloud application usage across the organization:
Visibility is the foundation of any CASB deployment. A CASB identifies every cloud application in use across your organization, including tools that employees, business units, and contractors adopted without IT’s knowledge.
Complete visibility helps you catalog which users access each app, how frequently they use it, and what data flows through it. This discovery capability helps security teams assess risk and make informed decisions about which apps to sanction, restrict, or block entirely.
Visibility matters because most organizations dramatically underestimate their SaaS footprint. Zylo’s data consistently shows that companies underestimate app quantity and spend by 1.7x and 3x, respectively. A CASB helps close that gap from a security perspective by surfacing applications that wouldn’t appear in a standard IT inventory.
The data security capabilities of a CASB prevent sensitive information from leaving your organization through cloud channels. This includes data loss prevention (DLP) policies that detect and block the sharing of:
CASBs can enforce encryption, tokenization, and access controls based on data classification, user role, device type, or location. These controls apply whether data is at rest in a cloud app or in transit between a user’s device and the cloud service.
CASBs detect and block external threats like malware, ransomware, and phishing that target cloud applications. They also use behavioral analytics, sometimes called user and entity behavior analytics (UEBA), to identify anomalous activity that could indicate a compromised account or insider threat.
If an employee’s account suddenly downloads an unusual volume of files or logs in from an unfamiliar location, the CASB flags the behavior and can automatically restrict access. This layer of protection extends your security posture into cloud environments where traditional endpoint tools have limited reach.
Cloud access security brokers help organizations maintain compliance with regulatory frameworks like HIPAA, PCI DSS, SOC 2, GDPR, and industry-specific standards. They do this by monitoring data handling practices across cloud applications and flagging activities that violate policy.
For regulated industries like healthcare, financial services, and government, CASBs help simplify the documentation requirements auditors expect by providing:
A CASB is deployed through two primary architectures: API-based and proxy-based. Each approach offers distinct advantages depending on your security priorities and infrastructure. Many organizations use a combination of both architectures to get the broadest coverage.
| Factor | API-Based CASB | Proxy-Based CASB |
|---|---|---|
| Deployment | Connects directly to cloud provider APIs | Intercepts traffic inline via forward or reverse proxy |
| Monitoring | Analyzes activity logs and data at rest | Inspects data in real time before it reaches the cloud |
| Latency | No impact on user experience | May introduce latency due to real-time processing |
| Device coverage | Limited to sanctioned apps with admin access | Can enforce policies on unmanaged devices |
| Best for | Monitoring sanctioned applications after the fact | Real-time protection and policy enforcement |
API-based CASBs connect directly to cloud service providers through their application programming interfaces. They monitor data at rest and user activity within the cloud application itself, without sitting in the traffic path between user and service.
API-based deployments are typically easier to implement and don’t introduce latency. They’re well-suited for monitoring sanctioned applications where you have administrative access. The tradeoff is that they operate after the fact, analyzing activity logs and stored data rather than intercepting traffic in real time.
Proxy-based CASBs intercept traffic between users and cloud services in real time, either through a forward proxy (which routes outbound user traffic) or a reverse proxy (which sits in front of the cloud application). This inline approach lets the CASB inspect, encrypt, or block data before it reaches the cloud.
Proxy-based deployments provide real-time protection and can enforce policies on unmanaged devices. However, they may introduce latency and can be bypassed if employees access applications through personal devices or networks that don’t route through the proxy.
CASBs address several security challenges specific to how organizations adopt and use SaaS applications today. Four use cases drive most deployments:
Cloud Access Security Brokers identify unsanctioned cloud applications by analyzing network traffic and cloud API data, surfacing tools that employees adopted without IT’s knowledge. Once discovered, IT can assess each app’s risk profile and decide whether to sanction, monitor, or block it.
Shadow IT discovery is one of the most common reasons organizations deploy a CASB. The scale of the problem is significant. The 2026 SaaS Management Index found that companies add an average of 9 new tools per month, and business units and individuals now account for roughly 9 in 10 apps by count.
Pairing CASB data with financial discovery gives you the broadest view of your portfolio, since network-based detection alone misses apps purchased on personal devices. Organizations that combine both methods are better positioned to eliminate shadow IT before it creates security or compliance exposure.
Using CASBs prevents sensitive information from leaving your organization through cloud channels by applying data loss prevention (DLP) policies that detect and block unauthorized sharing of:
 Financial records
Financial recordsProtecting sensitive data has become increasingly relevant as AI tools enter the environment. The 2026 SaaS Management Index found that 43% of IT leaders cite exposure of sensitive data or intellectual property as their top AI-related concern, and 77% discovered AI-powered features or applications operating without IT’s awareness.
CASBs can restrict employees from pasting proprietary information into unsanctioned AI tools or uploading regulated data to unapproved cloud storage services.
Cloud Access Security Brokers give security teams granular control over how data is shared with vendors, partners, and contractors through cloud platforms. They can:
Without these controls, employees can inadvertently expose sensitive files through collaboration tools like shared drives, messaging platforms, or project management apps. CASBs apply policies based on user role, data classification, and recipient domain, so your team can collaborate externally without creating unmonitored data flows.
CASBs automate compliance monitoring across cloud services by tracking data-handling practices and flagging activities that violate regulatory frameworks such as HIPAA, PCI DSS, SOC 2, and GDPR.
The 2026 SaaS Management Index found that only 21% of applications are behind SSO, which means authentication standards remain inconsistently applied across most organizations, a compliance risk that CASBs can help mitigate.
The primary role of a cloud access security broker is security. It does not address financial and operational governance, leaving your SaaS portfolio half managed.
The primary outcome of SaaS Management is cost savings, however CASBs do not provide visibility into:
That gap is costly. Zylo’s 2026 SaaS Management Index found that organizations carry an average of $19.8M in annual license waste. Business units and individuals now account for roughly four in five dollars of SaaS spend.
None of that waste is visible through a CASB, because it lacks access to financial data, contract details, and usage metrics. Security visibility alone doesn’t reduce spend or prevent redundant purchases from compounding year over year.
Structural blind spots of a cloud access security broker result in only a partial view of the applications in your portfolio.
It assumes traffic routes through the corporate network or a managed proxy. Employees working from home on personal devices can bypass the CASB entirely, meaning network-based SaaS discovery alone will leave gaps.
Financial discovery methods, which follow purchase data rather than network traffic, catch applications that network monitoring misses entirely.
To manage your SaaS portfolio beyond security, IT teams should pair a CASB with a SaaS management platform to help:
A CASB and a SaaS management platform (SMP) serve fundamentally different purposes, but together they give you complete visibility and control over your cloud environment. Here’s how they compare:
| Capability | CASB | SaaS Management Platform |
|---|---|---|
| Primary focus | Security and access control | Spend optimization, licensing, and governance |
| Discovery method | Network traffic and cloud API monitoring | Financial data, SSO logs, expense reports, and direct integrations |
| Key questions answered | Is this app safe? Is data at risk? | Is this app worth what we’re paying? Are licenses being used? |
| Blind spots | Misses apps accessed on personal devices or off-network | Does not enforce security policies or block threats |
| Stakeholders served | Security and IT operations | IT, procurement, FinOps, and software asset management |
The difference is that an SMP focuses on SaaS spend optimization, license optimization, and governance, while a CASB handles security enforcement and risk scoring for cloud traffic. Running both together gives you the most complete picture of your software portfolio.
Together, these tools help you:
For example, Zylo integrates directly with CASBs, as well as financial systems and identity providers like Okta and Entra ID. These integrations combine security signals with financial and usage data to give IT, procurement, and software asset management teams a unified system of record.
A cloud access security broker answers questions like:
An SMP answers questions like:
Security and cost governance are linked problems. Every unmanaged application, whether it’s an unsanctioned AI tool or a redundant SaaS subscription, introduces both financial waste and security exposure.
CASBs are an essential part of your cloud security stack. But without the financial visibility, license optimization, and governance that a SaaS spend management strategy provides, you’re solving only half the problem. The organizations that manage both security and spend most effectively are those that pair these tools and build cross-functional visibility across IT, procurement, and FinOps.
Request a demo to see how Zylo works alongside your cloud access security broker to give you complete control over your SaaS environment.
CASB stands for cloud access security broker. Gartner coined the term in 2012 to describe security solutions that sit between users and cloud service providers, enforcing enterprise security policies.
A CASB works by monitoring and controlling traffic between users and cloud applications. It deploys through API connections to cloud services, inline proxies that intercept traffic in real time, or a combination of both. Once deployed, a CASB applies security policies, detects threats, prevents data loss, and provides visibility into cloud application usage across the organization.
The four pillars of CASB are visibility, data security, threat protection, and compliance. Visibility uncovers all cloud apps in use, including shadow IT. Data security prevents unauthorized sharing through DLP and encryption. Threat protection detects malware and compromised accounts. Compliance helps organizations meet regulatory requirements like HIPAA, PCI DSS, and GDPR.
A CASB focuses on security, enforcing access policies, protecting sensitive data, and detecting threats across cloud applications. A SaaS management platform focuses on financial and operational governance, including spend visibility, license optimization, renewal management, and application rationalization. CASBs answer “Is this app safe?” while SMPs answer “Is this app worth what we’re paying for it?” Most enterprises benefit from running both.
A CASB supports SaaS discovery by analyzing network traffic and cloud API data to identify applications employees are using, including unsanctioned tools that IT hasn’t approved. This network-based discovery is one of several methods organizations use to build a complete SaaS inventory. Financial discovery, which tracks purchases through expense reports and accounts payable, catches applications that bypass the network entirely, making it a valuable complement to CASB-based discovery.
ABOUT THE AUTHOR

Ben Pippenger
Ben Pippenger is Staff Product Manager and Co-Founder of Zylo, where he helps enterprises maximize the value of their SaaS investments. With more than 20 years of experience in B2B software, Ben is a recognized thought leader in SaaS Management, license optimization, and IT strategy. Before founding Zylo, he held product and account leadership roles at Salesforce and ExactTarget. A self-proclaimed SaaS geek, Ben regularly speaks on topics like shadow IT, SaaS ROI, and software lifecycle management.

Table of Contents ToggleTL;DR: FinOps Cloud Cost Optimization Expands in ScopeWhat...
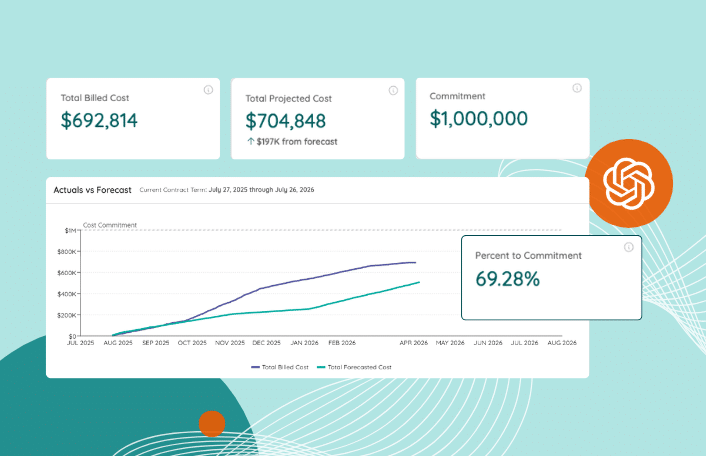
Table of Contents ToggleIntroducing Zylo’s Consumption Cost Management SolutionSystem of Record...

Table of Contents ToggleWhat Is a Cloud Access Security Broker?Why Organizations...

Table of Contents ToggleWhat Is a Cloud Access Security Broker?Why Organizations...
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |