
How to Control OpenAI API Costs Before They Escalate
Table of Contents ToggleWhat Is OpenAI API Pricing?Usage-Based Pricing vs. Subscription...
Back
Back
Search for Keywords...
Blog

Table of Contents
Updated February 5, 2026 with new data.
Shadow IT refers to the unsanctioned use of IT devices, software, applications, and services outside the ownership or control of IT. Some organizations embrace it while others despise it. If you fit into the latter category, the question often remains: how do we eliminate shadow IT? Before getting into the ‘how,’ it’s important to understand why it happens in the first place.
Shadow IT (as well as shadow AI) is just another way of saying applications bought by employees. Often, these employee-led purchases are made on a credit card and expensed. Our data shows a significant portion of your stack are apps purchased by individuals. In fact, they comprise 33.5% of your stack. So, why are they circumventing purchasing policies or “going rogue”?
“Someone’s spinning up some SaaS tool and it ends up being shadow IT. It’s not malicious. It’s someone trying to solve a problem.”
— Brad Pollard, CIO
Shadow IT spawned from the ambitious drive for efficiency, convenience, and innovation. It appears like a beacon of agility in an otherwise bureaucratic IT environment. While employees are well-intentioned, there are hazards that go undetected.
The cost of shadow IT applications is often the first risk companies think of and address. On average, companies spend $55.8M a year on SaaS and employee SaaS purchases make up 3.6%. While only a small portion of your total spend, it can quickly add up depending on the size of your organization.
Even scarier are the potential vulnerabilities these applications bring into the business. In many cases, shadow IT and shadow AI tools do not meet the standards set by IT departments. They’re often hidden from enterprise security systems, putting the entire company’s data at risk. Our research shows that 59.3% of expensed software have “Poor” or “Low” security risks scores, as measured by Netskope’s Cloud Confidence Index.
On top of that, shadow IT creates inefficiencies. Since IT doesn’t know about these apps, they’re often not behind single sign-on and aren’t connected to other systems. Redundancy often runs rampant, with duplicate apps and users with access to multiple apps that do the same thing. Employees’ search for productivity backfires, forcing data and collaboration to occur in silos. With AI tools added to the mix, it creates another layer of complexity to data security.
Despite even the best efforts, there’s no full-proof way to get rid of all the shadow IT in your stack. That’s because SaaS is ever-changing. In fact, organizations average six new applications entering their environment each month. But, there’s still hope.
Eliminating shadow IT requires a concerted effort and a judicious blend of policy enforcement, employee education, and embracing innovative IT solutions to effectively deal with shadow IT. In short: SaaS governance.
Shadow IT detection means identifying software, cloud applications, and other tools used by employees that were not approved through official IT channels. Without detection, businesses are vulnerable to poor budgeting forecasts, duplicate functionality, and potential security and compliance issues.
Key methods for shadow IT discovery include:
Shadow IT discovery is most effective when it combines several methods. A tool might appear in network logs but not in expense reports, or an employee might use a SaaS app without accessing it through the corporate network. Using diverse discovery methods provides a complete view of unapproved applications.
An effective detection system relies on multiple data sources rather than a single approach. Pairing technical monitoring with financial and human intelligence ensures you uncover more than just unapproved tools. These comprehensive methods also reveal the reasons behind shadow IT. Understanding why employees use unapproved tools is as important as identifying them.
Many shadow IT purchases occur through reimbursement channels. Employees sometimes subscribe to a tool, pay with their own credit card, then submit the cost as an expense.
Why expense report analysis works:
However, expense line items are often quite vague. Zylo data shows that up to 51% of software expenses are miscategorized and appear under unrelated categories like “Office Supplies” or “Meals.”
This is why financial discovery is a must. AI and machine learning-powered financial discovery can detect hidden SaaS expenses by integrating with expense systems, then identifying and categorizing spend, even when descriptions are unclear.
Additionally, integrating expense data with contract and license information allows IT teams to optimize business spending. For example, detection platforms can determine whether employees are paying for apps already covered under enterprise agreements.
Network traffic analysis is one way to detect shadow IT. It involves reviewing logs and monitoring outbound connections to highlight unknown or suspicious destinations, especially cloud services that have not been authorized.
Traffic analysis tools can identify patterns like frequent logins to file-sharing platforms or frequent API calls to SaaS services outside the IT catalog. Keeping track of these patterns over time helps pinpoint applications that are widely adopted in certain teams or locations without IT approval.
For example, if you see repeated traffic to a domain associated with a file-sharing service your IT team has never approved, it could signal an unsanctioned application. Network monitoring tools can also detect abnormal data transfer volumes to indicate possible data exfiltration risks.
A Cloud Access Security Broker serves as a gatekeeper between users and cloud services. CASBs enforce security policies, provide visibility into cloud usage, and generate detailed activity logs.
When utilized correctly, a CASB can:
CASBs are valuable when it comes to shadow IT detection because they not only uncover unknown tools, but they can also help enforce policies in real time. According to our data, unsanctioned apps tend to carry low or poor security scores, and a CASB can help reduce that exposure.
Advanced CASBs can also integrate with identity management systems so that business leaders can better understand which users are accessing specific services. By combining CASB data with other discovery methods, IT can develop a comprehensive profile of shadow IT activity and respond quickly to risks.
Often, the most effective shadow IT detection tool is communication. Employees may be willing to share the tools they use if they understand the reason behind the inquiry and trust that IT will help them find secure and approved alternatives.
Surveys and interviews can:
When combined with SaaS management data, employee feedback creates a more solid picture of your environment and enables cooperation between IT and business units.
Regular conversations with employees also help IT professionals understand why shadow IT occurs. Common reasons include workflow inefficiencies, unavailability of needed features in approved tools, or faster adoption timelines for essential tasks. Addressing the root cause of the issue can prevent future shadow IT and improve employee satisfaction and productivity.
How the Zylo Discovery Engine Powers the Most Comprehensive SaaS Management Platform
Learn MoreOrganizations use a variety of tools to uncover shadow IT, each with strengths and limitations depending on the environment, the types of SaaS in use, and the organization’s overall goals. In general, detection tools provide visibility into unsanctioned applications, usage analytics, and integration with IT systems, but no single tool can cover every scenario.
PROS
CONS
The Zylo SaaS Management Platform takes a comprehensive approach to shadow IT detection by combining discovery, financial analysis, and usage tracking in a single platform. Its AI-powered Discovery Engine identifies 100% of SaaS applications, whether purchased through IT or by individual employees.

By unifying financial, usage, and contract analytics, Zylo moves organizations beyond simple detection. IT teams can consolidate redundant tools, reduce risk, and make more informed decisions about SaaS investments. The platform ensures that new applications are automatically categorized, reducing manual effort while maintaining security and compliance.
When reviewing potential detection tools, consider the following to make sure you choose a solution that meets your organization’s needs:
By focusing on these criteria, IT teams can select a detection tool that not only uncovers shadow IT but also supports cost optimization, compliance, and proactive governance.
The pervasiveness of shadow IT in organizations provokes significant concern for IT leaders. By circumventing approved channels, shadow IT presents a range of risks – from security vulnerabilities to regulatory compliance issues. Acknowledging these issues, a comprehensive strategy is necessary to curb the practice. Various mechanisms, such as policy changes, IT infrastructure improvements, and leveraging new technology like a SaaS Management Platform, can play a crucial role in successfully eliminating shadow IT.
Read on for three strategies to eliminate shadow IT or watch the video.
Business units create shadow IT and adopt SaaS applications to meet business goals. As a result, these buyers often overlook the risks of shadow IT. With this in mind, it’s important to note that best practices begin with the source: the SaaS buyer.
When IT builds relationships with SaaS buyers and understands their needs, they can help remove the obstacles and empower the business unit.
“It’s become so much easier to sign up for a service or software. Educating end users of the risks when they’re using software outside of whatever’s available within their company’s catalog is really important.”
— Shravya Ravi, Head of Software and IT Hardware Asset Management at LinkedIn
Through active collaboration, IT can work with business leaders to think like a CIO. That mindset enables them to identify and adopt the technology that will support business goals and enterprise-wide advancement. Collaboration also creates a framework for shared goals regarding SaaS application cost, value, and security.
The bedrock of eliminating shadow IT is SaaS governance. Establishing policies and procedures can mitigate the use of unsanctioned applications within the enterprise.
More and more, IT, Software Asset Management, and Procurement leaders are turning to a governance approach we like to call Freedom within a Framework. In short, it ensures the right controls are in place without stifling employees’ ability to get the tools they need to be productive and innovate.
When it comes to shadow IT, having an expense policy is a great starting point. For instance, AbbVie has put measures in place to reduce shadow IT and waste in its stack. Depending on your organization and culture, you may want to set:
Evolving Your SaaS Governance Framework for the Digital Workplace
Learn MoreAnother lever is to standardize your software catalog. Software standardization is a component of SaaS governance where you establish a catalog of preferred software for your business. Typically, it’s part of a broader, business-led initiative to standardize business processes and data across a large, global enterprise.
A software catalog helps employees understand what software is available and enable them to request new tools if they’re not there.
Beyond helping eliminate and prevent shadow IT, standardization also helps:
Adobe Drives Innovation and Massive Savings with Zylo
In the past 4 years, Adobe has rapidly scaled from $9B to $18B. This growth has made an already complex environment even more complex. Learn how they leveraged Zylo to get complete visibility into their SaaS portfolio, unlock millions in cost savings and avoidance and improve the employee experience.
Once you have complete visibility into your SaaS inventory and implemented governance, it’s time to take action.
Start by identifying which apps you already have an enterprise agreement for. Understand if licenses are available and migrate the user or users under that contract. Before canceling the other subscription, make sure you understand the terms and renewal date. That will be critical for knowing when you can pull the plug, so to speak.
What if you don’t already have an enterprise agreement? We recommend notifying end users that they’ve purchased software outside of policy. You should request that they cancel the subscriptions, or potentially risk not getting reimbursed on future payments. From there, you can direct them to your application catalog to select an already approved tool. Be sure to provide direction on the process they should follow to request the purchase of a new tool if that fits their needs better.
Once you’ve done all this hard work, the last thing you want is for shadow IT to creep back into your environment. That’s where monitoring comes in. Your SMP is a helpful tool here, as you can set up alerts for when new apps or payments enter the system. It becomes easy to flag those that are against policy. Then, you can take quick action to eliminate that shadow IT app.
Ongoing governance paired with inventory visibility makes it easier to respond to potential shadow IT before it becomes a major risk. It requires education and collaboration to be successful, though. When employees understand the security, cost, and compliance implications of shadow IT, they’re more likely to adopt approved tools and follow proper procurement processes.
Take a look at these real-world case studies that illustrate the value of having a comprehensive shadow IT detection system in place. These examples showcase how visibility and governance translate to cost savings and risk reduction.
Zylo’s real-world case studies illustrate the value of comprehensive shadow IT detection. These examples demonstrate how visibility and governance translate to cost savings and risk reduction.
Adobe scaled its business from $9B to $18B over four years—with software sprawl growing with it. To tackle shadow IT, Zylo provided full visibility into Adobe’s portfolio, helping standardize the company to 400 approved apps from nearly 2,500.
Employees now request software exclusively through the enterprise store, and policies prevent purchases via expense, eliminating unapproved tools. This approach identified redundant applications, unlocked millions in cost savings, and improved the overall employee experience.
AbbVie used Zylo’s services to implement expense thresholds and SaaS governance, achieving dramatic results in just one year. By linking purchase data with approved tools, the company reduced expense spend by 47% and canceled over 60 subscriptions that violated policy, optimizing spending and improving compliance across departments.
Effectively managing shadow IT requires visibility, governance, and collaboration before unapproved applications put your company at risk. Technical monitoring, financial tracking, and employee engagement help identify hidden tools, reduce security threats, optimize costs, and boost operational efficiency.
Continuous oversight ensures new applications are discovered and evaluated as they enter your environment. By enforcing policies, maintaining a standardized software catalog, and leveraging SaaS Management Platforms like Zylo, your organization can proactively reduce risk, stay compliant, and protect productivity.
Take control of shadow IT today. Learn how Zylo can help and request a demo to see it in action.
“Shadow IT detection” refers to the process of identifying software, cloud services, and applications used in an organization without IT approval. It combines technical monitoring, financial tracking, and user feedback to uncover unsanctioned tools.
Detecting shadow IT is essential in terms of preventing security risks, compliance issues, and unnecessary expenses. Without accurate visibility, organizations can’t ensure effective governance or safeguards for sensitive data.
Common methods include:
Layering these approaches provides a more complete view of unapproved applications.
Tools like Zylo provide visibility, usage analytics, and financial insights that help identify unsanctioned SaaS applications.
Organizations can prevent shadow IT by establishing clear policies, maintaining an approved software catalog, and continuously monitoring new tool usage. Education and collaboration with involved departments also help guide users to approved solutions.

Table of Contents ToggleWhat Is OpenAI API Pricing?Usage-Based Pricing vs. Subscription...

Table of Contents ToggleTL;DR: FinOps Cloud Cost Optimization Expands in ScopeWhat...
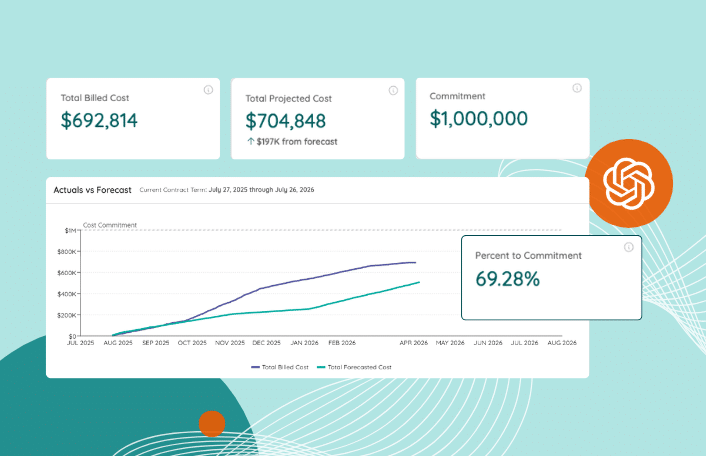
Table of Contents ToggleIntroducing Zylo’s Consumption Cost Management SolutionSystem of Record...

Table of Contents ToggleWhat Is Shadow IT?Shadow IT Detection MethodsPros and...
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |