What Is Shadow IT?


Updated on March 11, 2026 with new dataSaaS is easy to buy—almost frighteningly so. Go to any website, click a button, and punch in your credit card number. Voila! You’re in.
We all have a co-worker (or two) who has done this, which may seem innocuous. But the reality is that one in fifteen (6.6%) employees in your organization is expensing software. This leads to what we call shadow IT, and at a time with swift AI adoption in the workplace, shadow AI.
What is shadow IT? In this blog, we’ll define what it is, where it comes from, the pros and cons, and how to eliminate it.
What Is Shadow IT and Where Does It Come From?
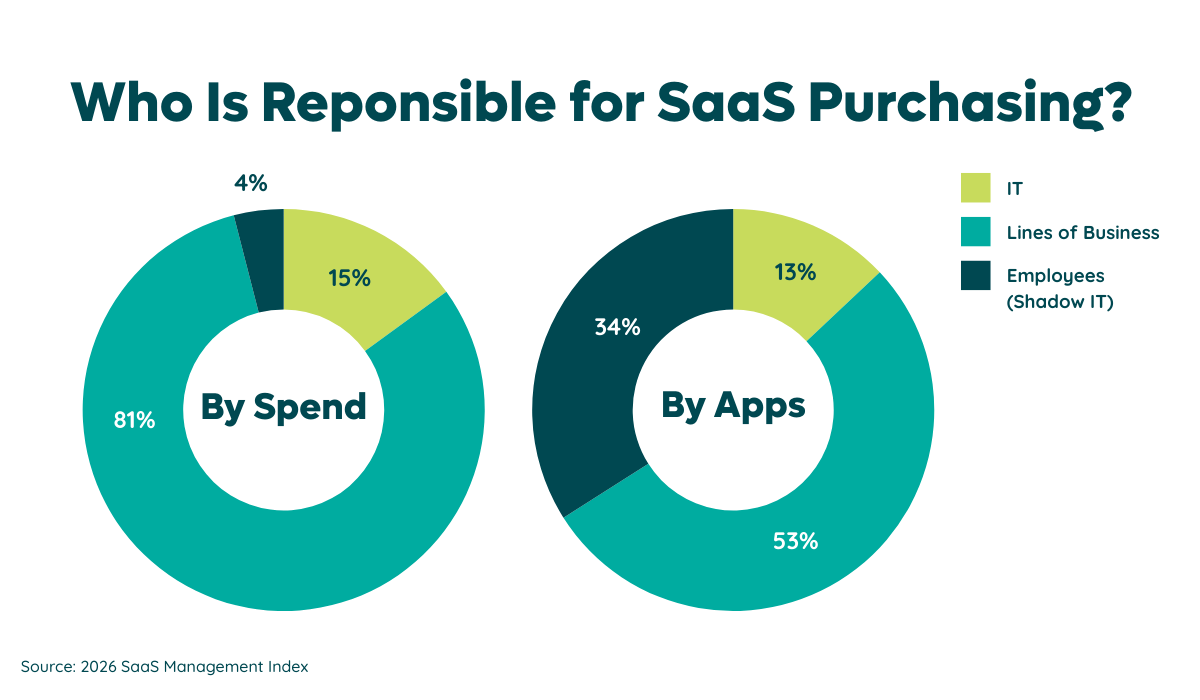
Shadow IT, also known as shadow applications, is software purchased by individuals or lines of business without IT’s knowledge. Zylo's 2026 SaaS Management Index found that shadow IT accounts for just 4% of an organization’s SaaS spend. However, it amounts to a significant 34% of your SaaS portfolio. Something’s out of line, right?
How do you identify those shadow applications to optimize and reduce them? First, it helps to figure out where it comes from. Shadow IT has three main sources:
- Employee purchases. Often, they purchase software ad hoc because they are either unaware that a tool already exists in the company’s SaaS stack or because they bypass the company’s procurement process or purchasing policies to get what they want/need.
- Hybrid and remote work. The new way of working has made shadow IT more prevalent. It began when organizations had to quickly “tool up” in the pandemic. Now employees need tools to stay connected and collaborate from anywhere.
- Redundant applications. Apps with functionality around online training, collaboration, and project management are the most common shadow applications, accounting for the most redundant functions within a business’s software portfolio.
Pros and Cons of Shadow IT
Before we look at combating shadow IT, let’s look at all the effects it can have on your SaaS stack and SaaS spending—for good and for ill. While shadow IT carries financial and security risks, it also has benefits that justify its existence.
Potential Benefits of Shadow IT
We’ve spent most of this article discussing how scary shadow IT is, so you’re probably doubtful of our claim that it can benefit your company. Let’s prove our point. Shadow IT has three main benefits
- It drives innovation. Sometimes, your company just doesn’t have the SaaS a team needs to do their job to the best of their ability. Shadow IT allows employees to acquire the tools they need when they need them to do their jobs better and faster.
- It empowers employees. If you entrust your employees with acquiring the tools they need, they will be more productive and more satisfied in their roles. Forrester reported that two-thirds of Gen Z and Millennials consider autonomy in their apps, services, and devices as a top work priority.
- It drives IT productivity. IT managing what SaaS can and can’t come into the company takes work time. Shadow IT removes their role as gatekeeper, and that allows them to get back to projects that are just more impactful and important. Plus, this frees them up for IT emergencies.
Shadow IT Risks
Alongside those benefits, shadow IT has its fair share of risks — trust us. Between unvetted apps, untracked purchases, and unprocessed security policies, shadow IT can pose huge threats to your company’s security and spend. Shadow IT has three main risks you need to keep in mind.
Multitude of Increased Cost Factors
We could talk all day about the increased cost of shadow IT, but we’ll try and boil it down to a few key points:
- Ad hoc purchases mean duplication of apps and mischaracterized software. If your company spends a million dollars on Slack, you might also discover thousands of dollars of expense reports to Slack. This is just wasted, duplicated spending for duplicated subscriptions.
- Uncontrolled, unknown costs make budgeting a nightmare. You can’t manage what you can’t see, and you can’t budget for what you can’t control. Shadow IT drains your SaaS budget and can prevent you from having the funding you need to buy impactful tools.
- Shadow IT prevents you from planning for renewals, meaning you come to the negotiation table without the tools and data you need to negotiate a good contract. Or, even worse, an employee will unknowingly sign an auto-renewal contract that leads to a small, constant drain on your SaaS budget.
Data Breach Threats
Shadow IT means applications aren’t being vetted by your IT department. Yet, SaaS applications almost always deal with your business’s data. In fact, Zylo's 2026 SaaS Management Index shows that expensed software (a.k.a. shadow IT) are riskier. Nearly 59% have "Poor" or "Low" Cloud Confidence Score, or risk score.
%20-%202026%20SaaS%20Management%20Index.png)
On the surface, employee purchases may seem innocuous and harmless. But that truth is that they pose more risk thank you think.
Shadow IT can be seriously damaging to your company, because it opens you up to potentially devastating data breaches. That’s not even mentioning the ones that happen just because of human error! IT vetting applications can save your company a whole lot of money and trouble.
Decreases Regulatory Compliance
Alongside risks of data breaches, unvetted applications can lead to your company unwittingly breaching regulations, most notably the Health Insurance Portability and Accountability Act (HIPAA) and the General Data Protection Regulation (GDPR). This can cost you a ton in fines and legal issues.
How to Eliminate Shadow IT
To eliminate shadow IT, you must first identify it. With the process of SaaS inventory management, you can discover and tracj shadow applications. Then, limit shadow IT by actively monitoring it.
Achieve Visibility into Purchases
While you could look at your expense reports to find unsanctioned software purchases, you won’t find everything. That’s because 51% of expenses are miscategorized as something other than software.
Ongoing discovery is critical to uncover those hidden apps. Multiple methods exist for discovering and inventorying shadow applications and their attributes, including:
- Manual spreadsheet inventory: Cost-effective but they're time-intensive and often create data and collaboration silos.
- Single Sign-On (SSO): Great for managed tools, but fails to track unmanaged tools.
- Web browser plugins: Employees can bypass these easily.
- Cloud Access Security Broker (CASB): Fails to monitor data from personal devices.
- Financial analysis: Effective, but can suffer from human error.
- AI-powered matching model: relies on pattern behavior, using machine learning to identify both known and unknown SaaS applications. It's a robust choice for SaaS discovery.
By following the money, regardless of the procurement process, organizations can identify a comprehensive view of their shadow IT spending. No matter what tool you use, visibility is key. So the more effective the tool, the better.
Many businesses now utilize SaaS management tools like Zylo, which provides a near 100% accuracy for SaaS detection and categorization.
Build Relationships with SaaS Buyers
Once you’ve uncovered your SaaS stack, you can build relationships with SaaS buyers in your company and get them in line with an overall strategy. Start by identifying the SaaS stakeholders and establish connections with them.
Building these relationships helps you establish trust and communication. It results in unifying stakeholders on your strategies and tactics, and supports an open door policy where they they can reach out to you with questions and concerns related to SaaS.
Define a Governance Strategy
With visibility achieved and stakeholders unified, you have all the information and perspectives you need to build a governance strategy.
While SaaS purchasing is decentralized, we’re seeing more and more IT organizations centralize SaaS governance. Having policies that regulate software purchasing keeps IT in the loop and reduces shadow IT and its associated costs.
“Freedom within a Framework” is an effective approach where parameters are established to avoid opening the organization up to unnecessary risk or spend. At the same time, it also enables employees to have the freedom to choose their tools.
Defeating (or Befriending) Shadow IT
No longer do you have to ask: what is shadow IT? It’s a natural occurrence in any organization.
Sure, it has its risks. But for some companies, the benefits outweigh the risks if they have visibility into their entire SaaS estate.
When you have complete visibility and establish and communicate governance policies, you can reduce compliance, security, and financial risks while still empowering employees to unlock productivity, creativity, and collaboration.
Shadow IT can be your friend, you just need to set boundaries with it.
If you want to maximize visibility and take the next steps with your company’s shadow IT, you need the right tools. Learn how Zylo’s AI-powered Discovery Engine can detect shadow IT in your organization.