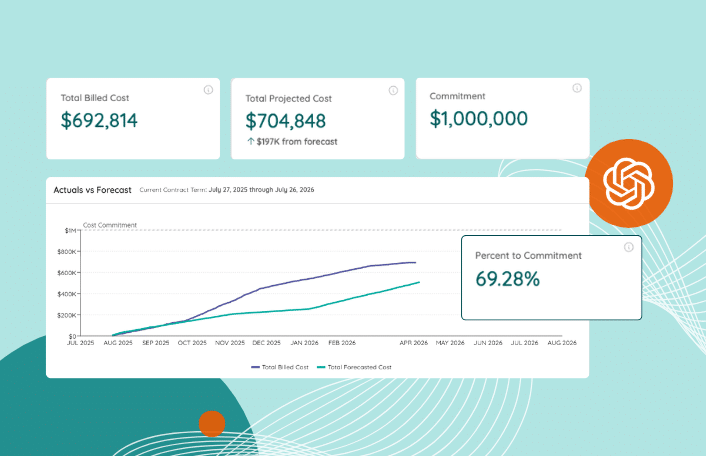
Stop Cost Overruns with Zylo’s Consumption Cost Management Solution
Table of Contents ToggleIntroducing Zylo’s Consumption Cost Management SolutionSystem of Record...
Back
Back
Search for Keywords...
Blog

08/18/2016
Table of Contents
It’s no wonder CIOs and IT departments around the world are concerned with the amount of data stored in 3rd party cloud environments. Enterprise companies, regardless of industry, often have hundreds if not thousands of subscription software applications that they manage, and the number of applications the average organization adds to its tech stack continues to grow at a steady rate each year. But if CIOs and IT departments don’t have proper visibility into or control over the technologies its employees are using, then they have every right to be concerned about security matters and sensitive customer or employee data.
According to the report entitled, The 2016 Global Cloud Data Security Study, “…Roughly half of all cloud services and corporate data stored in the cloud are not controlled by IT departments, two-thirds of sensitive data stored in the cloud is left unencrypted, and more than half of companies are not proactive in their compliance with privacy and security regulations for data in cloud environments.”
The proliferation of “Shadow IT” is classically defined as, “Information-technology systems and solutions built and used inside organizations without explicit organizational approval. It is also used, along with the term ‘Stealth IT’, to describe solutions specified and deployed by departments other than the IT department.” However, Shadow IT can also occur when individuals in an organization just aren’t aware of other applications or solutions used in other departments — it isn’t always correlated with the classic definition above.
The concept of Shadow IT isn’t a new term to technology departments, but as more and more employees and teams are empowered to purchase SaaS software on their own — either through a traditional contract process or even via a company or personal credit card — the more Shadow IT can pose a threat to data stored in 3rd party cloud environments. But Shadow IT is becoming just a way of life for organizations and is very difficult — if not impossible to control. For IT executives, it’s best to cast a light on these applications and embrace them with Zylo’s SaaS optimization platform.
The rise of the subscription economy is continuing to shift and pivot the way organizations conduct business . Across all industries, employees and contractors are more connected than ever before, customers and patrons expect a higher level of service, and executives and management teams have data available at their fingertips to make the best decisions for the business at any given moment. These innovations have allowed everyone across the spectrum of business — whether B2B or B2C — to operate more efficiently and with better accuracy.
Because SaaS applications are often so easy to purchase and implement into current business processes often requiring just a few clicks of a button, a credit card, and a computer or mobile device in which to open a browser, employees are skipping the procurement process. Employees and teams are making seemingly innocent and small purchases on their own. After all, is a $39/month contract really worth bothering IT about? And until recently, most companies have looked the other way.
But the concern for IT departments is that they’re losing visibility and control of the entire organizational tech stack, removing the ability to make the most economical decisions for their organization, and to protect important data and personal information.
Results from The 2016 Global Cloud Data Security Study suggest that, “Many of these problems stem from the growth in shadow IT taking action beyond the reach of corporate governance. According to the survey, nearly half of cloud services are deployed by departments other than corporate IT, and an average of 47 percent of corporate data stored in cloud environments is not managed by the IT department.”
For IT teams without complete insight into the applications its organization is using, Shadow IT can cause issues in the form of compromised data, redundant systems, underutilization, and over spending. Add on top of that the employee confusion when individuals aren’t sure of what system to use and what the protocols for each system entail. Executives rely on the power of systems like SSO and Cloud Access Brokerage companies that help with security, but what about visibility into other important aspects?
CIOs and IT departments need visibility and control into their entire SaaS tech stacks, not only to own the procurement and decision process for new applications and renewals, but most importantly to help guide individuals and departments during the purchase process. When IT departments gain complete visibility into the technologies each department, team, or individual is using, it helps everyone across the organization make more economical decisions, but most importantly double down on important security measures.
The subscription economy is radically changing the way all organizations across all industries do business . None of us can imagine life without the platforms and applications we rely on each and every day across all areas of business. But for CIOs and IT executives, it’s time to understand how SaaS is being leveraged across the organization, gaining a real-time understanding of spend, utilization, and feedback. Imagine how much more powerful those subscriptions could be and how much more secure the organization and its data would be if the power were fully unlocked for technology teams?
Zylo is the leading SaaS optimization platform that transforms how companies manage and optimize the vast and accelerating number of cloud-based applications organizations rely on today. The platform provides an online command center for all cloud-based software used across a company, giving an organization visibility into what software is used, how much is spent and how to optimize their cloud software investments.
Interested in unlocking the power of SaaS at your organization? Visit zylo.com to sign up for our newsletter or follow @getzylo on Twitter for more information.
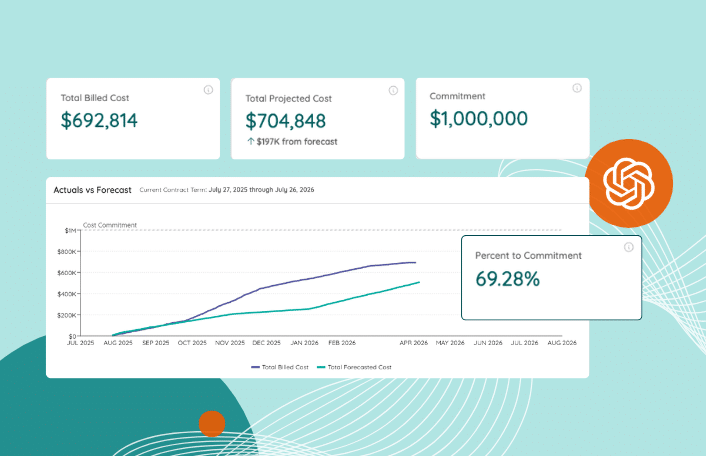
Table of Contents ToggleIntroducing Zylo’s Consumption Cost Management SolutionSystem of Record...

Table of Contents ToggleShadow IT is a Growing ConcernVisibility & Control...

Table of Contents ToggleShadow IT is a Growing ConcernVisibility & Control...

Table of Contents ToggleTL;DR: SaaS Compliance Is a Visibility and Governance...
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |