Reveal Shadow IT & Shadow AI to Mitigate Risk
AI tools are accelerating shadow IT faster than organizations can track. Zylo continuously discovers new applications across financial, identity, and operational systems—providing the visibility needed to uncover shadow IT and AI before they create security, cost, or compliance risks.
Identify & Remediate Shadow IT
Discover
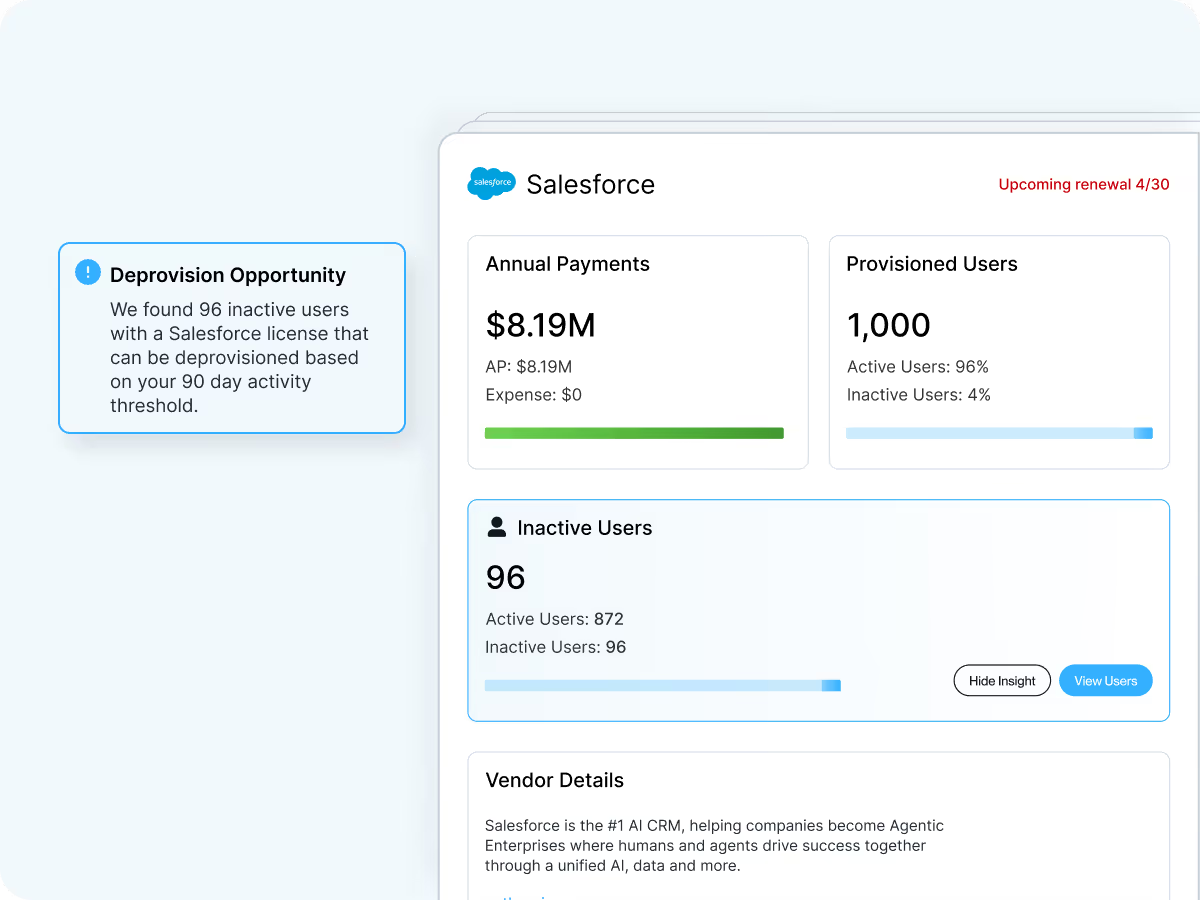
See who purchased the application, which tools were expensed, and how much was spent.
Inspect
Analyze discovered applications alongside spend and usage data to understand adoption and risk.
Take Action
Take steps to approve the application, consolidate it with an existing tool, or eliminate it entirely.
Discover Shadow IT with Multi-Source Detection
Connect Zylo’s discovery engine to spend signals across accounts payable, expense systems, resellers, marketplaces, and other financial data sources. Zylo’s AI-powered matching models uncover and categorize new applications.
Centralize Your Software Data in a Single Place
Bring application, spend, usage, and contract data into a single inventory that you can trust with a reliable view of every application across the organization.
Monitor Software Adoption in Real Time
Track discovered applications, ownership, and adoption trends with interactive dashboards. See emerging shadow IT and AI tools early so you can intervene before risk and redundancy spread across the organization.
Stop Shadow IT Before It Creates Risk
Unknown applications create hidden risk across your SaaS environment. Identify unmanaged tools, reduce security exposure, and bring every application under governance.